Apple Macbook air remote wipe recovery
Remote Wipe
Apple has a security feature so that if your apple device is stolen it can be remotely wiped, and so there is no danger of your security being compromised. Is it safe, and can the data be recovered.
On the basis of one such example, and also a similar report from an American journalist, the answer is that the wiping is not complete, and much data can be recovered. Our customer had a Mac that was in effect blank and so no access to the data. In order to recover any possible data it was necessary to create an image of the internal disk drive, or logical storage.
Disk image process.
The Macbook Air is a very slim device and does not contain a standard disk drive. Many contain SSDs. Also the problem of cracking the case open is not for the faint hearted so to obtain an image of the hard drive, the Apple was booted with Linux. This process is simple (and there are probably several ways of doing this).
- Create a bootable Ubuntu DVD (DVD image is downloaded from http://www.ubuntu.com/download (Version 12 was used in this case).
- Insert DVD in Apple, or external DVD drive. On power up press the ‘c’ key, and the apple will boot off the Ubuntu disk.
- Supply an external (probably USB) disk drive large that the internal drive capacity
- Make sure the external drive is clean to prevent any data contamination.
- From Ubuntu determine the drive device names and the do a ‘DD’ from the internal drive to the eternal drive. An example might be
- sudo -i
- dd if=\dev\sda of=\dev\sdc - This was a slow process and there may be a better command
- The final result will be an image of the Mac drive on the external drive
What was on the drive
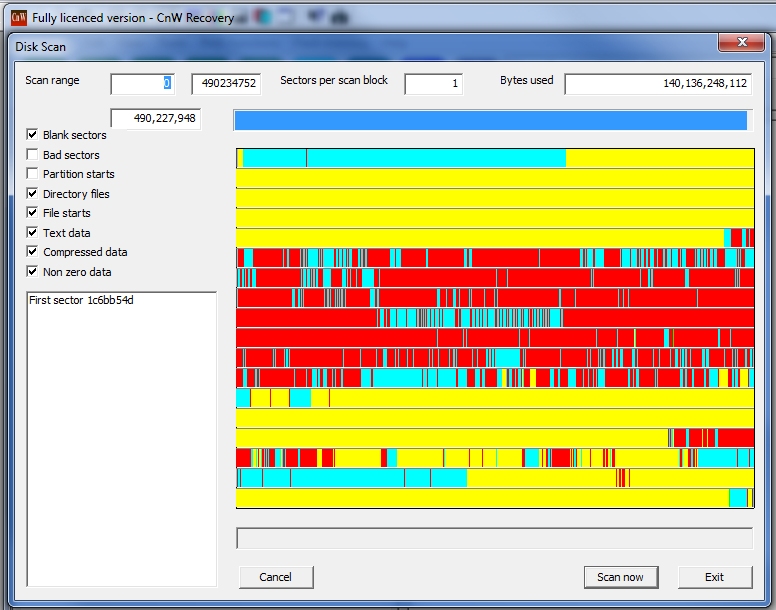
Yellow - blank sector. Cyan - Compressed data, or a sector with more than 200 different byte values.
Red - a possible file signature, will be the start of file with data carving
For a good disk one would expect to see the start with many files (mainly compressed data, cyan) but with many file starts (red line). On the recovered image the compressed data started at sector 0x64028 which is where the file system normally starts. There was an area of random data (could also be encrypted, but not possible to tell). Then the disk is padded to about 64GB with blank sectors. This means that for the 251GB disk drive, the first 25% has been wiped, and no recovery will be possible. The rest of the disk does contain data.
Data recovery
The examination above shows that the first 25% of the has been wiped, and this will contain most of the directory structure of the disk. Thus the only way to recover data is with data carving. The CnW data carving routine found many thousands of photos, and the majority were not fragmented. There were also many good videos.
Will this always work?
It is not possible to say if this process will always work. The curious fact is that on the example we saw, and the one reported in America, both had the same 64GB of data overwritten. It was suggested that was the amount that was written before the process was stopped. It could however be that it is all that is overwritten. It does look as recovery of 75% of data may be possible, although with the restrictions of data carving. CnW does though often product filenames containing the date of a photo, or title of an MP3 or DOCX file even when data carving. Download demo here.
With SSDs, there may always be a problem of TRIM commands working in back ground removing data
|